How to use the Zoom malware safely on Linux if you absolutely have to
Zoom is malware… if you have to run it, run it in its own prison.
Update (8 Jul, 2020): I ended up doing my talk over our Vimeo Live account instead.
You can watch the edited recording on our web site.
We gave the folks in the Zoom meeting a link to my talk and they watched it there. I then did Q&A in the Zoom meeting via my iPhone (where Zoom is sandboxed). Don’t forget that anywhere on the Internet is just one link away. You are not stuck to using a certain venue just because a conference organiser is using it.
If you must use Zoom – sadly, it is one of the few options if you want to use simultaneous translation or have a sign language interpreter – do so using the web interface as that’s safer (the web interface is sandboxed by the browser). Failing that, use the app on iOS as that is also sandboxed.
TL; DR: Use Jitsi or something else instead
You should be using Jitsi instead. (Or, if want to live stream to lots of people, pay for something like Vimeo Live if you can.)
“But I’m forced to use Zoom!”
When I agreed to speak at Creative Mornings Istanbul tomorrow, I didn’t know they were holding the event over Zoom. I guess it’s fitting that the series I’m speaking at is called Insecure.
As I use Linux, I’m going to take every precaution I can before running the Zoom malware on my machine. That means two things: using AppArmor and Firejail.
-
Install Firejail.
sudo apt install firejail firejail-profiles -
Enable AppArmor for Firejail.
If you’re on an Ubuntu-based system, you should already have AppArmor enabled but you may not have its utilities installed (I didn’t on Pop!_OS 20.04).
First, install the utilities:
sudo apt install apparmor-utilsThen, apply the AppArmor profile for Firejail:
sudo aa-enforce firejail-default -
Fix the Firejail profile for Zoom.
Out of the box, the profile that comes with Firejail did not work for me. Zoom was stuck on its “connecting” message.
To fix this, we must override some of the default settings:
# Ensure local settings folder exists for Firejail. mkdir -p ~/.config/firejail # Add the custom settings to it. echo "protocol unix,inet,inet6,netlink\nignore seccomp\nseccomp \x21chroot" > ~/.config/firejail/zoom.local -
Make a separate home folder for Zoom to use.
We don’t want Zoom to have access to our actual home folder so let’s create one it can use in its place:
mkdir -p ~/.zoom -
Test it out.
Now test it out and ensure that everything works:
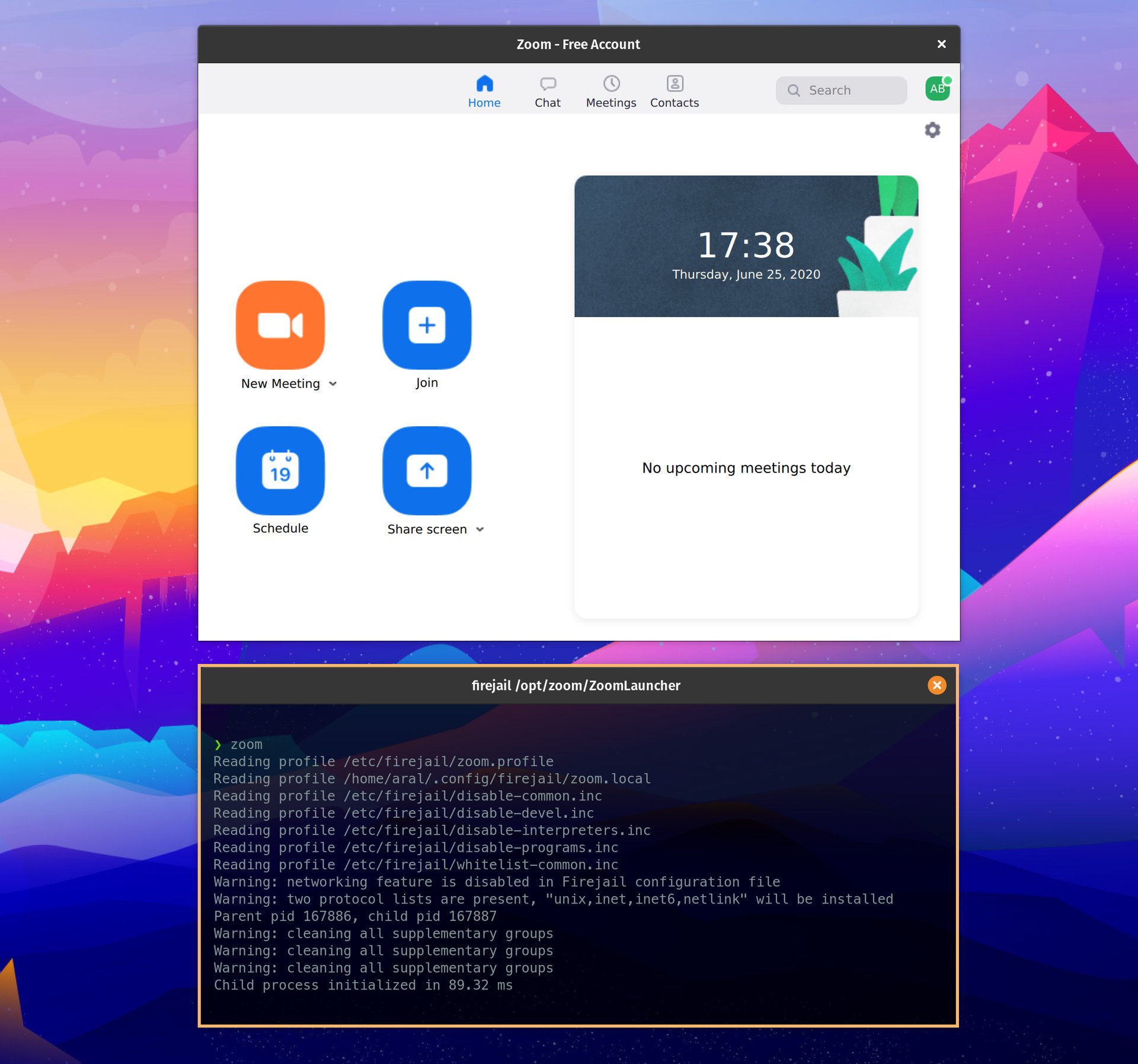
firejail --apparmor --private=$HOME/.zoom zoomIf it all works, there’s just one more step to go.
-
Replace the Zoom shortcut.
Everytime we launch Zoom, we want it to launch in its sandbox and we don’t want to keep having to remember to use the Firejail command so let’s replace the Zoom shortcut with our own little script:
sudo rm /usr/bin/zoom sudo me=$HOME bash -c 'echo -e "#!/bin/bash\nfirejail --apparmor --profile=/etc/firejail/zoom.profile --private=$me/.zoom /opt/zoom/ZoomLauncher" > /usr/bin/zoom'Now, whenever you want to start Zoom relatively safely (nothing is entirely safe), you can simply open up a Terminal window and type:
zoom
I went to all this trouble because I need to be able to present tomorrow using Zoom. In the future, I’ll be asking ahead of time if an event uses Zoom and, if so, I won’t be speaking at it.
At the very least, I do not want to be the reason that people install malware on their computers and use a system that violates their privacy and human rights.
Friends don’t let friends use Zoom
For event organisers: respect the privacy of your speakers and attendees and to not subject to surveillance and malware by Zoom.
You have viable alternatives like Jitsi and Vimeo (and many others)… use them.
If you must join a Zoom meeting, try to do so using the web interface as that’s safer (the web interface is sandboxed by the browser). Failing that, use the app on iOS as that is also sandboxed.
But remember that no matter how you use Zoom, your messages are not end-to-end encrypted and everything you do is monitored by Zoom and most likely by the Chinese government also.
PS. Even if you do all this, you won’t be able to join the meeting from your sandboxed Zoom if the event organiser has registrations turned on for the event. I stopped trying after this (see the update, above).