Hypha Spike: Diceware
Pulled out from Hypha Spike: DAT 1.
Design
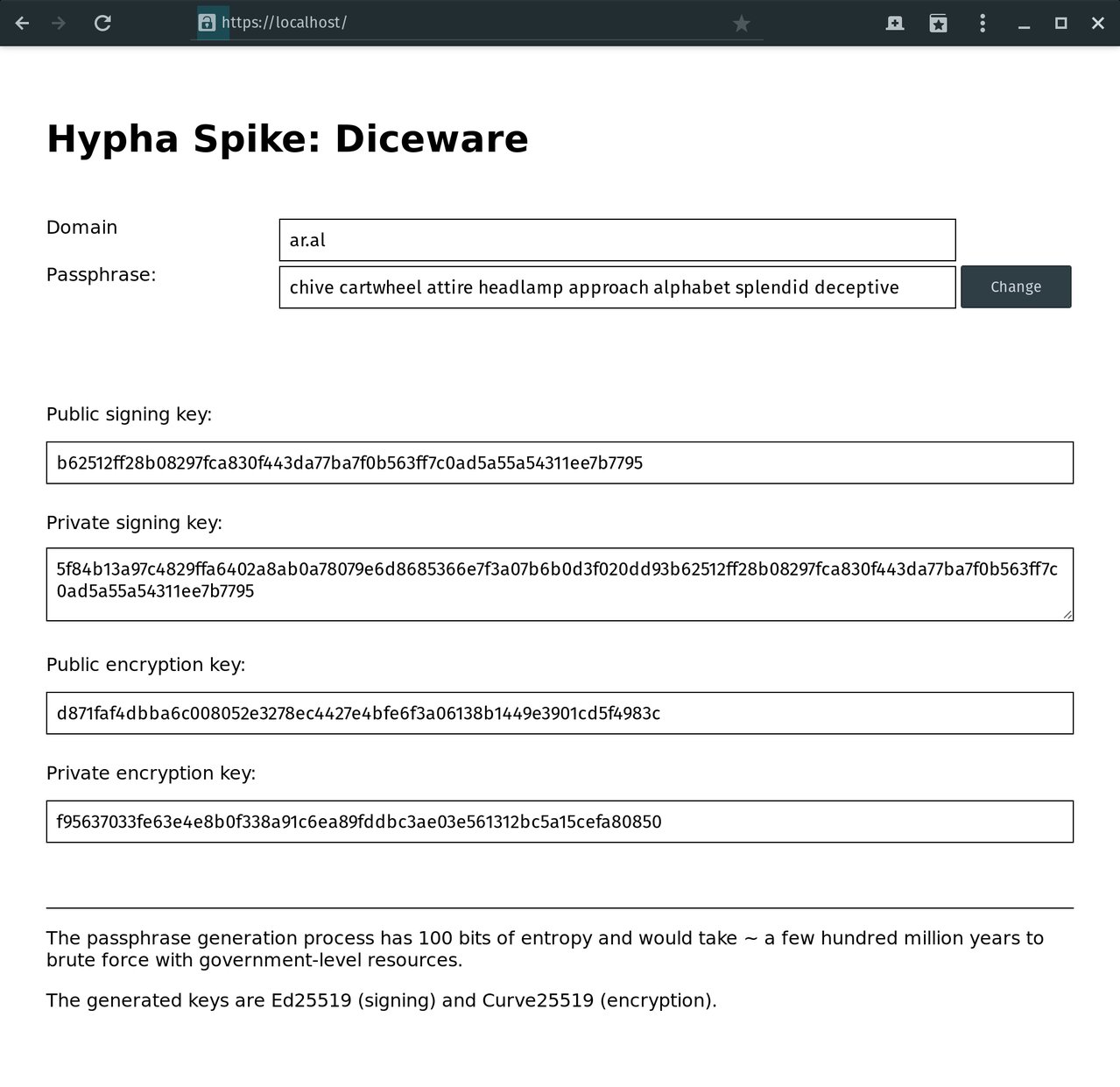
Screenshot of the completed spike.
-
Use Diceware for passphrase generation to ensure a high-entropy process.
-
Use budo in the spikes to enable lightweight use of bundling/modules/etc.
Postmortem
Pulled this out into its own Spike so that it doesn’t clutter the DAT 1 spike.
Starting with the Aspect Setup 1 spike, in this spike I:
-
Refactored to use budo so I can use requires, etc.
-
Was getting an error in budo due to Chokidar on Linux:
Error: Cannot find module 'fsevents' from '…/node_modules/chokidar/lib'Ended up upgrading dependencies for budo (pull request) and also squashing this error as the error is in error (pull request). We will, of course, not be using budo in production but it’s fine for the purposes of this spike.
-
Started generating passphrases using Diceware and EFF’s New Wordlists for Random Passphrases
References
- xkcd: Password Strength
- Excellent explanation of above xkcd. Quote: “Security at the expense of usability comes at the expense of security.” – AviD
- Passphrases that you can memorize — but that even the NSA can’t guess
- Diceware (Source code)
- EFF’s New Wordlists for Random Passphrases
- eff-diceware-passphrase